Work with NFC tags was first put into operation at DonbasEnergo
NFC tags. NFC tags have huge potential. The main advantage of NFC compared to other wireless technologies is its low cost and the ability to use in a wide range of tasks. And taking into account the simplicity of the scheme and a small number of elements, tags can be produced in huge quantities at low cost. Last year, this method was first implemented at Donbassenergo.
How it works?
NFC-enabled devices support three modes of operation: reader / writer, peer-to-peer communication, card emulation.
Card Emulation Mode
Card emulation mode allows NFC-enabled devices to work like smart cards.
In card emulation mode, an NFC-enabled device communicates with an external reader, like a regular contactless smart card. For example, when making a payment using an NFC-enabled device.
P2P (Peer-to-peer) mode
Peer-to-peer mode allows two NFC-enabled devices to communicate with each other to exchange information and files so that users of NFC-enabled devices can quickly exchange contact information and other files with one touch. For example, users can exchange Bluetooth or Wi-Fi connection settings or exchange data, such as virtual business cards or photos.
Read / write mode
Read / write mode allows NFC-enabled devices to read information stored in NFC tags (or tags) embedded in smart posters and displays, or interact with another NFC device in read / write mode. The initiating device can read data from the second device or write data to it.
Using tags, you can read transport schedules, gain access to special promotional offers, read travel tags and routes, and more.
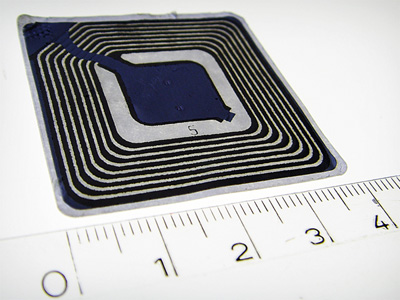
NFC technology works in an active chip and in a passive tag. For the latter to work, you do not need to use energy, so regular charging is not necessary. Note that the NFC tags are of minimal size, there will be no problems with their placement, you can even wear them in the keychain. Each tag is an antenna that has the thickness of a paper sheet. Only 0.1 s is needed for data exchange. To start the exchange, simply attach a tag to the smartphone at a distance of no more than 5 centimeters.
Foreign companies are quite actively taking advantage of electronic identification. Each accounting object is assigned a unique number, which allows for individual control of equipment instances. World experience in implementing RFID shows that in such critical industries, such as oil and gas and mining, the cost of equipping RFID tags and RFID equipment (readers and antennas) is several times lower than the amount of damage from accidents that RFID technology can prevent.
The hardware of a typical hardware-software complex consists of the following elements:
- RFID tags, protected from shock, abrasion, exposure to chemically active environments, high and low temperatures, moisture, capable of working on metal objects.
- A set of mobile and stationary RFID readers.
- Communication channels (industrial Ethernet, RS232 / 485, Wi-Fi).
- A server for processing and storing data about objects, issuing data to the operator’s workstation (AWP) or dispatcher.
- AWP of the user, dispatcher and operator – a computer to which RFID equipment is connected.
Identification objects can be: pallets, returnable metal containers, barrels, packaging products, repair and production equipment, drilling rigs.
RFID tags in a durable plastic case with a high level of dust and moisture protection are convenient for use in difficult climatic conditions, and are optimally suited for use in industries, mines, quarries, factories, and construction sites. It is used to identify containers, loading equipment.
RFID is actively used to control repair equipment, industrial equipment and other technical means. Asset control and identification is an effective method of optimizing the work of construction and repair equipment.
What allows RFID?
- To carry out the search and operational accounting of equipment, products, containers.
- Verify the authenticity of objects.
- Track the movement of equipment, products, containers online.
- Track inspection history, carry out equipment specifications.
- Monitor and determine the degree of equipment wear.
- Reduce the risk of theft and abuse.






